InfluxDB Endpoint Security State Template
By
Darin Fisher
updated December 14, 2025
Product
Use Cases
Developer
Navigate to:
Our team recently discovered an exposed endpoint without authentication enabled, though we know it had previously been required. The root cause was a missing configuration as a result of a recent upgrade a few weeks earlier, and was easy to fix by simply enabling the configuration parameter correctly.
We needed a way to catch this type of issue quickly going forward, for this and for other public endpoints, which should be secure by default. Here is how we solved it.
A complete monitoring system should continuously verify that the security controls are functioning as expected and have not changed. Here we see how to track the state of our web service authentication and SSL certificates with the InfluxDB Endpoint Security State Template.
This will tell us:
- Is the service available?
- Is the SSL certificate still valid?
- If authentication is required, is it turned on and functioning?
Service availability is one of the many metrics used for both security and operations. One example where availability is a security concern is a DoS (or DDoS) attack. The purpose of such an attack is to render a service unavailable.
The SSL certificate validation can also be used by operators to assist in certificate renewal automation. For security purposes, we need to regularly validate that our identity and service security precautions are functioning properly.
When authentication is required, we should continually verify that it is active and functioning properly. A bug, misconfiguration, or hack attempt are a few of the possible causes for authentication to be failing, and possibly letting everyone have access.
We recommend utilizing a dedicated service account for authentication validation. The account should have read-only access to the minimum level of services required to function.
Set up the InfluxDB CLI environment; from the command line run:
influx apply --template-url https://raw.githubusercontent.com/influxdata/community-templates/master/endpoint-security-state/endpoint-security-state.ymlThe Telegraf configuration will need to be updated with the URLs and credentials for the endpoint(s) you wish to monitor.
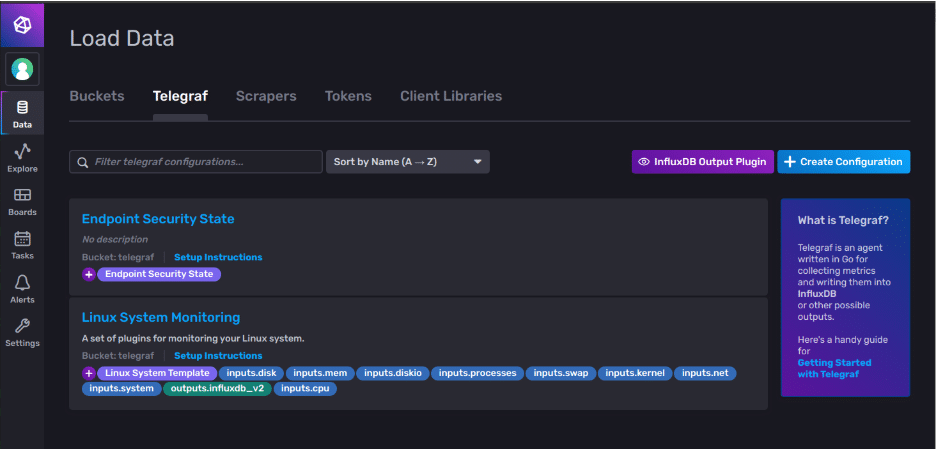
Download the Telegraf template, from the navigation window in the InfluxDB UI, select Data?Telegraf. From here, select the configuration, “Endpoint Security State” and download the file to your system.
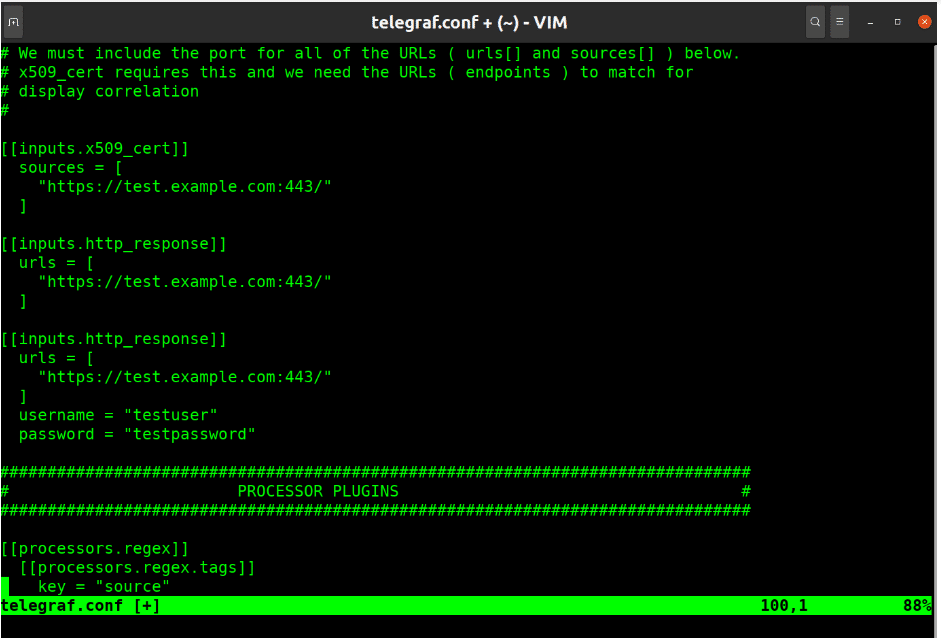
Let’s take a deeper look at the Telegraf config (shown above). It uses multiple input plugins and the Regex processor to normalize the data a bit.
The x509 Cert plugin collects various metrics from the site’s certificate. This only supports the HTTPS schema.
The HTTP Response plugin is utilized for connection and authorization attempts.
For authorization testing, make sure to configure each endpoint with and without credentials. We need one to fail for validation.
Verify the URL is not redirected to another site for authentication if it is enabled.
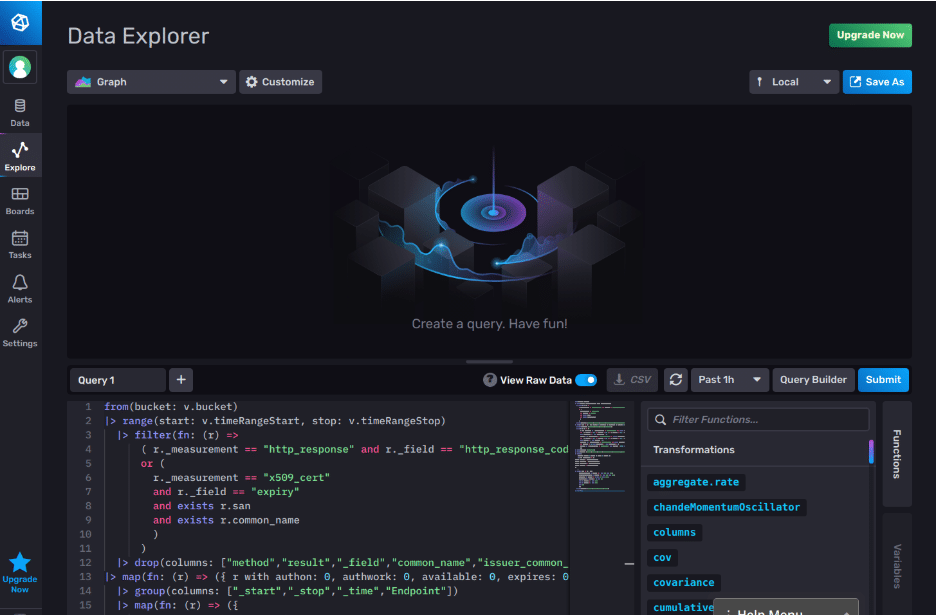
The Flux query uses the response status code to determine the various states. Any successful status or authentication failure response indicates the service is available. An authentication failure response indicates authentication services are available. Successful responses indicate authentication is functioning properly.

The resulting table will display each endpoint and an icon to indicate the state for each metric:
- ? The service or function is as expected.
- ???? The site's certificate will expire in less than 30 days.
- ???? The service or function is in a failed or unexpected state.
- ? We were not able to derive the state.
This could be extended with alerts for failed authentication services or expired certificates.
We could collect the Apache or NGINX performance metrics, add an endpoint variable along with a couple of histograms to give the user a more complete picture of the services.
As for me, I really enjoy the ability to quickly build solutions on the InfluxDB platform. Not so long ago, I would cobble together a solution, start evaluating 3rd party solutions or move the problem to the “get this done when I have extra time” queue.
So go ahead and play with the InfluxDB Endpoint Security State Template, and let us know if you have any questions, on our InfluxDB community site or Slack.
